When discussing data protection and security, you often hear the term “industrial espionage”. Federal agencies or our oh-so-important business associations keep warning us:
Over the last few years, industrial espionage increased dramatically!
And, of course, the focus of said espionage is on German enterprises and their know-how.
The same sentences can also be read in a survey done by “CORPORATE TRUST – Business Risk & Crisis Management GmbH”.
You can access it through the following link . It is rather worth reading, especially with respect to how you can make people fearful?
You will find the warning that “cyber war has become reality a long time ago” and that it “has arrived in the middle of our society”. Neither can the “computer worm Stuxnet“ be ignored. After all, it was “probably developed especially in order to sabotage the control mechanism Simatic S7 – which controlled the frequency converter of the motors in Iranian nuclear programs.”
(Note the word “probably”).
To be sure, the exact goals of the customers were unknown, but the complexity of the attack shows that we went from an era of script kiddies and crackers towards a new dimension of danger – etc.
 Mind you, these are all original sentences taken from the study. The very choice of words in its martial character already makes me sceptical.
Mind you, these are all original sentences taken from the study. The very choice of words in its martial character already makes me sceptical.
Regardless of this, I take the subject of data theft a lot more seriously than, for example, the fear of personal data being abused. I also believe that “stolen” data will help you to reach your goal faster than having to develop “something new”.
I have a vivid memory of a project we did a little less than 30 years ago. We were asked to develop something totally new. Except that we did not have the slightest idea how the “new” could be done. In those days, studying the sources the competition used was quite helpful. And to this day, I do not know if we made use of said sources legally or, maybe, in a certain shady area.
Still, I do not think industrial espionage is quite as menacing as it is projected – and not only in the internet. One of the reasons I give for this is that these fear-inspiring studies originate with firms which want to sell special counter-espionage services and products. And, of course, federal agencies and business associations are quite ready to chase the pig through the village. After all, there is nothing else they are busy with. What a nice idea to employ James Bond! Isn’t it a beautiful shiver you feel whenever you hear how evil the world is and how you yourself are absolutely powerless?
But let us remember what it used to be like!
 When I worked for Siemens, we were absolutely prohibited to take any secret documents with us when we left the building complex. And almost everything was secret. Consequently, there was a random generator at the portal. Occasionally, it lit up. When it did so, you had to open your briefcase and show what was inside. It went without saying that taking pictures on the factory premises was not allowed.
When I worked for Siemens, we were absolutely prohibited to take any secret documents with us when we left the building complex. And almost everything was secret. Consequently, there was a random generator at the portal. Occasionally, it lit up. When it did so, you had to open your briefcase and show what was inside. It went without saying that taking pictures on the factory premises was not allowed.
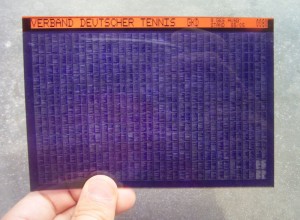
Those were also the times when we used those blue “Micro-Fiche-Films”, along with the reading devices that went with them. Micro-Fiche, or rather microform is the first technology I know which you could use for storing many data on little material. For us, it was usually sources of complete operating systems that were stored on a small square of film so we could carry it around with us in our briefcases.
Of course, it was not realistic that the secret papers were never leaving the factory premises. For one thing, our firm was quite distributed. Some data were needed when you went to see a customer. And once in a while, you also wanted to do some work at home. Consequently, we had permission papers. If you had this paper, you were permitted to take any secret paper you needed. The higher echelons – I do not remember up from which AB or GB level you qualified – were also permitted to take secret documents without the permission paper. I also do not remember if AB truly was short for “departmentally authorized“ and GB for “generally authorized“.
But then what a strange (and totally stupid) kind of firewall was that? It was certainly no more secure than the modern firewalls offered by IT?
Incidentally, the first two colleagues from the former GDR we employed directly after the re-unification confirmed this opinion. They came directly from Robotron Dresden. And they told us that, naturally, at Robotron, they always had the latest plans of the Siemens chip developers on their desks the moment they were made. Except they were not able to put them to any use. The necessary raw material (purest Silicium) could not be obtained in the GDR. Neither did they have the necessary tools to even produce the prototypes.
To be sure, I do not know if our ex-GDR engineers were just after spinning us a good yarn, but I can easily imagine that this is actually how it happened. Basically, I believe data will always end up where they should not be. But mostly it makes not the slightest difference, even if, perhaps, you get quite annoyed, and justly so.
But I also believe the methods changed. And the new methods are a lot more efficient, even though they have nothing at all to do with IT. Let us take a look a China, where, allegedly, the enterprises want to spy on Western firms. Do they really need to do that? Or are there, perhaps, far easier methods?
Here is what you can read in “invest in Bavaria” at “China in Bayern”
Currently, more than 130 Chinese enterprises, for instance Huawei Technologies, Pearl River Piano, ZTE, Yingli Solar, ET Solar and a little under 11,000 Chinese citizens reside in Bavaria. About a third of them live around Munich. Approximately 3,000 Chinese students at Bavarian universities further attest to how attractive the Bavarian universities are.
I also know that there are Chinese branches in the “regions with weak infra-structure“ in Bavaria that have such lovely scenery. Those Chinese branches specialize on R&D (research and development). Actually, these enterprises are quite heavily subsidized by the Bavarian authorities – and accordingly, their moving here is celebrated quite bombastically. Because, as a general rule, F&E is a clean sector. It does not damage the environment and attracts intelligent engineers.
And what is the first thing a Chinese F&E enterprise will do? No question! They lure away the German engineers formerly employed by their German competition. And the best ones at that! Those with exactly the kind of know-how most urgently needed in China. And the German engineers are happy to come. They are quite attracted to live cheaply in a nice place, do some F&E in a modern laboratory and mostly even be paid better than before. This is how the Chinese can choose from the best persons with the right knowledge. Now isn’t that a lot more efficient than having to crack networks and servers?
Neither can I find any fault with it. After all, we live in a globalized world and I rather like the Chinese with their friendliness and tasty cuisine… And I seem to remember “knowledge is the only raw material that grows as you share it“!
After all these ideas, I read the aforementioned “study” with totally different eyes. “Installing fear“, is, after all, a very successful marketing strategy…
RMD
(Translated by EG)
P.S.
I took the pictures from the central media archive Wikimedia Commons. They were taken by Nichtich and Tomasz Sienicki [user: tsca, mail: tomasz.sienicki at gmail.com]

